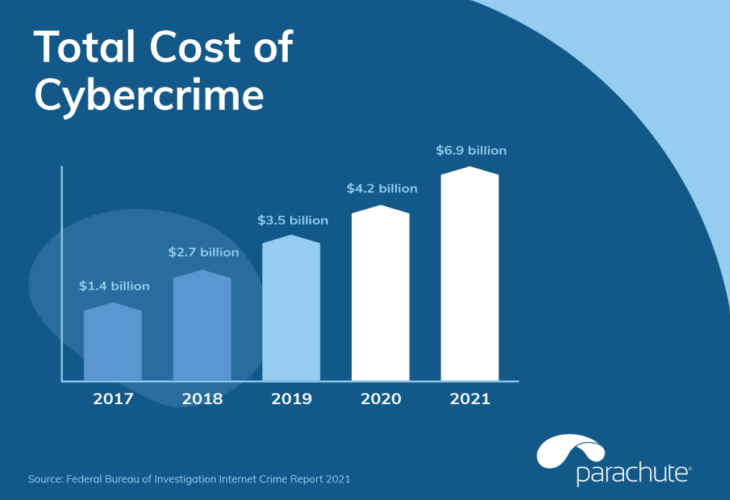
While the digital era has given businesses many advantages and new tools to use, it also comes with the risk of cybercrime and cyber-attacks. In fact, on average, a cyber-attack costs a staggering $4.35 million in 2022. Cybersecurity can be a never-ending game of cat and mouse; one side constantly trying to find ways to outwit and bypass the other.
While many data breaches are due to negligence or human error, many more are due to deliberate and malicious attacks by cybercriminals. Most human errors can be prevented or mitigated by solid internal policies and ensuring that your employees receive regular cybersecurity training to make them aware of potential risks.
There can be many types of network security, some of which will be applied by your ISP or network provider and some of which will be applied by you. Understanding the different types of network security and how they can benefit your business can go a long way in helping protect your organization from the increasing number of cyber-attacks.
What is network security?

Network security covers any tool or process an organization utilizes to protect its network and data from malicious cybercrime attempts. Different types of network security can include hardware, software, and cloud-based solutions. Their primary purpose is to block a range of cyber-attacks, and in the event of a data breach, contain the threat and prevent it from spreading. These tools can be implemented by your IT support team or outsourced to a company that takes care of your IT functions.
10 Types of Network Security
Knowing some of the types of network security that could help protect your organization can help you plan a network security strategy and take the first step to implement protection. A solid understanding of cybersecurity and the risks cyber-attacks pose to your business is essential for any organization.
1. Antivirus/antimalware
Perhaps the most commonly known security solution, comprise different types of software that protect your network from attacks by cybercriminals that seek to create a backdoor into your network so they can infiltrate it. Antivirus software protects your network-connected devices from infection. Antivirus software need the necessary updates regularly to cope with new threats. Antimalware programs seek out and eradicate any malicious programs that have managed to infiltrate your network.
2. Access authentication
Of the different types of network security, this one ensures that only authorized users can access your network, as well as restricting access to certain data and information. It can also check the device users are accessing your network from to ensure that the device is secure. There are several types of access authentication tools, including PAM (privileged access management), IaaS (Identity as a Service), and NAC (network access control).
3. Preventing DDoS
DDoS (Distributed Denial of Service) attacks are often directed at large corporations or governmental websites. In the third quarter of 2022 alone, cybersecurity provider Kaspersky’s DDoS Intelligence system detected more than 57,000 such attacks. DDoS prevention solutions are designed to identify and filter out illegitimate attempts to access your network so that your network’s integrity is maintained for legitimate users.
4. Email security
Email-related attacks like phishing are on the rise. In the second quarter of 2022, APWG observed over 1 million phishing attacks. It can be tempting for staff to click on an innocent-looking link, but by doing so, they risk introducing malware into your network. Good email security tools can help flag suspicious emails and attachments before they reach an employee’s inbox. It should be noted that, as well as robust security tools, you should also train your staff on email security.
5. Firewalls
Firewalls are commonly used on personal networks but may have higher levels of protection on business networks. They can comprise hardware and software that create a ‘wall’ between your network and any incoming traffic. You can set different rules and policies, if a sent data packet does not meet those rules, the firewall will reject it.
6. Device security
With staff often working remotely or on the road, they often use mobile devices for work purposes and may be using apps to contact colleagues or forward calls. When considering what types of network security you need, you should consider how many of your staff use mobile devices. A good solution can limit how much access these devices have to your network while also monitoring their vulnerabilities when using the network. An MDM (Mobile Device Management) solution can allow administrators to control access.
7. DLP (Data Loss Prevention)
Your data may not only be your organization’s lifeblood, but it can also be sensitive and highly confidential. You need to know how to protect your data. By utilizing good DLP tools, you can block any network users from misusing data or sharing it, whether maliciously or accidentally, outside your network. It can analyze all outgoing files and ensure that they meet any rules you have set.
8. App security
Your business probably uses multiple apps in different areas of your organization. These can include everything from apps for recording calls to CRM (customer relationship management) systems. Therefore, you want to be sure that each and every app is secure to use. Using app security solutions monitors how safe any apps used are. It can also ensure that all your apps are updated regularly, that any apps you use are protected against attacks, and that any vulnerabilities are identified and blocked.
9. Endpoint security
Of all the different types of network security, this can be an essential addition. It can ensure that every device connected to your network is protected from potential cyber-attacks. That can include everything from laptops and desktops to printers and mobile devices. Organizations seek to achieve endpoint security by combining a number of tools, including app security, network monitoring, and network access control.
10. Network monitoring
This encompasses a range of apps that monitor all traffic into or out of your network. The apps then flag and respond to unusual or potentially malicious traffic. Some of the most common types of network monitoring includes:
- SIEM (Security Information and Event Management): Can give you a detailed overview of all network activity and can provide a crucial log so that any breaches or malicious activity are easier to investigate.
- IPS (Intrusion Prevention Systems): Scans all the traffic on your network and can flag and block anything that violates your rules and policies.
- IDS (Intrusion Detection Systems): Similar to IPS, IDS focuses more on monitoring network packets and flagging anything suspicious so administrators can investigate.
The takeaway

Cybersecurity is essential, particularly in areas like medical or financial services security, but also for any business that handles sensitive data. With cybercrime on the rise, you need to choose security measures that can deal with current threats and adapt to new threats as they emerge. While we rely heavily on specialized tools, you should also recognize the potential risk from human error and develop policies to address this.
Your cybersecurity journey, as far as your website is concerned, should really start with your choice of domain. You should carry out a comprehensive audit of all your network security and identify any potential vulnerabilities so that you can use different network security tools to protect your organization.









